Read more »
A blog for Confluence group.
Tuesday, 22 September 2020
The NES And Famicom Accurate Cartridge Information Database
Read more »
Monday, 21 September 2020
Lords Of The Fallen Free Download
Lords Of The Fallen Free Download
Lords Of The Fallen PC Game 2014 Overview
Features of Lords of the Fallen
- Animations and graphics are amazing
- Action Role Playing game
- Player can take help of magic spells
- Latest technology weapons
System Requirements of Lords Of The Fallen PC Game 2014
- Operating System: Tested On Windows 7 64 Bit
- CPU: Core i 3
- RAM: 6 GB / 8GB
- Hard disk Space: 25 GB
Lords Of The Fallen Free Download
Saturday, 12 September 2020
Proper Analog Retro Video Capture With The Datapath E1/E1s
Read more »
Thursday, 3 September 2020
The EverDrive N8 Pro - Second Time Perfection? A Review
 |
| Your Choices (courtesy of krikzz) |
Sunday, 30 August 2020
Evilginx2 - Install And Configure In Localhost Complete
Related links
- Pentest Tools For Ubuntu
- How To Install Pentest Tools In Ubuntu
- Hack App
- Pentest Tools For Windows
- Pentest Tools Framework
- Hack Tools
- Hacker Tools Mac
- Physical Pentest Tools
- Hacking Tools Github
- Hacker Tools For Pc
- Termux Hacking Tools 2019
- Hacking Tools
- Hacking Tools Download
- Pentest Tools Download
- Hacking Tools For Mac
- Hack Tools For Games
- Hacking Tools Mac
- Pentest Tools Apk
- Underground Hacker Sites
- Hack Tools Mac
- Pentest Box Tools Download
- Hacking Tools Kit
- Pentest Box Tools Download
- Hacking Tools For Games
- Hack Tools For Windows
- Hacker Tools Apk
- Nsa Hack Tools
- Pentest Tools Alternative
- Hacking Tools And Software
- Hacking Tools For Windows Free Download
- Hack Tool Apk
- Hack Tools For Ubuntu
- Hacking Tools For Beginners
- Growth Hacker Tools
- Hacker Tools Apk Download
- Hacking Tools For Windows Free Download
- Hacker Tools Apk
- Pentest Tools Find Subdomains
- Best Hacking Tools 2019
- Hacking Tools And Software
- Bluetooth Hacking Tools Kali
- Hacker Tools Github
- Tools Used For Hacking
- Pentest Tools Alternative
- Pentest Tools Bluekeep
- Pentest Tools Tcp Port Scanner
- Pentest Tools Open Source
- Pentest Tools Subdomain
- Hacker Tools For Pc
- Hacker Tools For Windows
- New Hacker Tools
- How To Install Pentest Tools In Ubuntu
- Hak5 Tools
- Hacker Tool Kit
- Pentest Tools Bluekeep
- Hack Tools Github
- Github Hacking Tools
- How To Hack
- Hacking Tools Usb
- Tools 4 Hack
- Hacker Tools Apk Download
- Hacker Tools Apk
- Hacking Tools
- Hack Tools
- Hacker Tools Software
- Pentest Box Tools Download
- Hacker
- Hack Rom Tools
- Hacker Tools For Ios
- Kik Hack Tools
- Easy Hack Tools
- Hacker Tools Apk Download
- Pentest Tools Framework
- Pentest Tools Linux
- Hack Apps
- Hackers Toolbox
- Hack And Tools
- Top Pentest Tools
- Hacking Tools Pc
- Hacking Apps
- Hack Tools Mac
- Pentest Tools Website Vulnerability
- Pentest Tools Linux
- What Is Hacking Tools
- Hacker Tools Apk Download
- Hack And Tools
- Pentest Tools Alternative
- Hack Tool Apk
- Hacker Tools 2020
- Pentest Tools Find Subdomains
- Hacker Tools Hardware
- Hacking Tools For Games
- Pentest Tools For Android
- Hacker Tools For Ios
- Hacker Tools Software
- Best Pentesting Tools 2018
- Hack Apps
- Hacker Techniques Tools And Incident Handling
- Pentest Tools Open Source
- Hacking Tools Windows 10
- New Hack Tools
Blockchain Decentralized Application Hacking Course - A Journey Into Smart Contract Hacking And DApp Penetration Testing (Web 3.0)
Smart Contract Exploitation and Hacking Course Announcement
What Is this:
For those who have been hitting me up on twitter and YouTube for more blockchain smart contract exploitation content this blog is for you. I have posted a video below explaining what this is and included a course outline of the content we are providing free for everyone. I was actually told recently that I am crazy for giving out this level of detailed content and training for free.. However, I believe in the original hacker ethic code from long ago, that information should be freely available for everyone!! In this frame of mind, the only pay for content will be if you wish to go the extra mile. For the person who wants to prove to themselves or others that they learned something via a certification package with detailed exam prep targets and guides, followed by a final exam CTF and reporting write-up.
So I hope you enjoy this content. The content and walk through labs will be all free. This content will be posted regularly over the next few months 90% of it is already written and ready to go.
We will start off with the differences between Solidity and other languages and do a quick coding overview before we start hacking. This way everyone is on the same page when we start looking at coding examples of vulnerable targets or reviewing case study code. Then we will cover a wide range of typical issues that effect decentralized applications(DApps) and smart contracts on the Ethereum blockchain. How to spot them and exploit them with full walk-through style learning. Subjects we have already released (Re-Entrancy, Integer Attacks, Authorization) have been updated with new code, new examples, and case studies etc. Some of the learning content will be the same but with a lot of newly added content. And in the case of Authorization completely re-written and expanded on.
Basically this course was created to get the information out there in a clear concise way. Because when I started researching blockchain hacking all I found was a paragraph here and there on something that was overly technical or completely theoretical. I couldn't find any clear concise learning or examples. This drove me nuts trying to figure everything out, until I gave up and just coded my own vulnerabilities and hacked them. So hopefully this fills the knowledge gap to offer a clear and concise, Zero Fluff resource to those on the same path.
CTF Exam:
If you do enjoy this series over the next few months and want to challenge your skills and certify that you learned something we will be also offering pay for certification bundle that includes Decentralized Application (DApp) targets and detailed lab guides as preparation for a final exam against a more comprehensive CTF certification challenge target. More info on this as the months progress.
Bug Bounty of Sorts:
These labs are completed but we are working on a way to deliver the content which requires me to code up a course delivery software. So feel free to hack the course delivery software once its up, if you break in or bypass authorizations I will give you the full course for free provided you help me fix it. :P
Pre- Requisites:
This is more of a intermediate / advanced course with a white box code approach to bug hunting and a dynamic approach to application hacking and exploiting targets, with that said you will need the following pre-requisites:
- Ability to code in some language and understanding of coding concepts.
- Application hacking or development background with firm understanding of vulnerabilities
Contact Info:
As this is free, I only ask that you provide constructive feedback as we are creating other more advanced hacking courses on random subjects we are interested in. Most of which will be free. And feedback helps us not do things which are not useful and integrate new ideas where they make sense.
Cheers and I hope this finds you well.
Twitter:
Email:
- info@cclabs.io
WebPage:
Intro Video:
Course Outline / Release Order:
Orange = = Whats included additionally for the full course
Blue = = What will be released free in blogs / videos
(Mostly every Mondays) over the next few months
Building and Scoping Things
Chapter 1: Cliff Notes on Blockchain
Intro:
What is a Blockchain and how is it secured
Smart Contracts
What is a Decentralized Application (DApp)?
Diving into Blockchain Components:
Distributed Vs Decentralized
Provenance Use Case:
Consensus and Mining:
Hands on Lab - Blockchain Consensus walkthrough Lab
Summary:
References:
Chapter 2: Threat Modeling and Scoping Engagements
Architecture Considerations:
Business Logic Locations and Technology Decisions
Development Environments
Threat Modeling
Summary
References:
Chapter 3 – Solidity for Penetration Testers Part 1 (Hello World)
About Solidity
Hands on Lab - Remix interface overview
Structure of a Smart Contract
Hands on Lab – HelloWorld
Summary
References:
Chapter 4 – Solidity for Penetration Testers Part 2
Beyond Hello World
Hands on Lab – Code HelloWorld bank
Code Level Walk Through of HelloWorld Bank
Checks Effects Interactions:
Summary
Part 2: Hacking and Exploiting Things
Chapter 5 - Glass Half Full or Glass Half Empty: Integer Attacks
Underflows and Overflows
Withdraw Function Vulnerable to an underflow
Transfer Function Vulnerable to a Batch Overflow
Batch Overflow Code Explanation:
ERC20 Batch Overflow Case-Study
Walkthrough of The Vulnerable Function
Reviewing the Real Attack Transaction
Hands on Lab - Exploiting Our Own ERC20 Batch Overflow
Hands on Lab - Fixing the ERC20 Overflow
Exam Prep - DApp Target + Detailed Lab Guide
Hands on Lab -Safe Math Walk Through
Integer Attacks Summary
Integer Attacks References
Chapter 6 - You Again: Leveraging Reentrancy Attacks
Reentrancy Intro
Checks Effects Interactions Pattern
Simple Reentrancy Example Code
Passing the Checks:
Looping the Interaction:
Updating the Effects:
Attacking Code Example:
Hands on Lab - Attacking a Simple Reentrancy
Hands on Lab - Fixing the Checks Effects interaction Pattern
Send vs Transfer Vs Call.Value
Case Study – The Dao Hack
Exam Prep - DApp Target + Detailed Lab Guide
Reentrancy Summary
Reentrancy References
Chapter 7 Do You Have a Hall Pass: Access Control Attacks
Understanding Smart Contract Authorization and Visibility
Visibility:
Simple Visibility Example:
Implementing Authorization:
Example Walk-through of No Authorization
Thinking about Smart Contracts as unpublished API's for DApps
Case of the Video Game Heist
Enumerating functions in a contract
Hands on Lab - Directly Calling Public Functions with Web3
Hands on Lab - Example Fix with Simple Authorization
Exit Scam Warning
Hands on Lab - Example Fix-2 Using Modifiers for Simple Authentication
Hands on Lab - Example Using Openzeppelin for Role Based Access Control
Exam Prep - DApp Target + Detailed Lab Guide
Authorization Summary:
Authorization References
Chapter 8 - Dude Where's My Data: Storage Vs Memory Attacks
Intro - Not Written Yet – Up Next
Code Example - Not Written Yet – Up Next
Case study? - Not Written Yet – Up Next
Exploiting vulnerability - Not Written Yet – Up Next
Summary - Not Written Yet – Up Next
References - Not Written Yet – Up Next
Chapter 9 - Do I know you: TxOrigin vs Message.sender Attacks
What's the difference?
Man In the Middle Via tx.origin
Hands on Lab - Simple tx.origin Example Walkthrough
Hands on Lab - Vulnerable TX.Origin Example Walkthrough
Exam Prep - DApp Target + Detailed Lab Guide
Action steps to familiarize yourself with the contract:
Attack Options:
Summary
References
Chapter 10 - Who Am I: Delegate Call Attacks
How delegate calls work:
Delegate Call vs Call
Simple Delegate Call Example Code
Simple Delegate Code Example Walkthrough
Hands on Lab - Simple Delegate Example Walkthrough
Variable Memory Issues with Delegate Calls
DelegateCall Storage Simple Example Code
Hands on Lab - DelegateCall Storage Walkthrough
Exam Prep - DApp Target + Detailed Lab Guide
Case Study - Parity Wallet Attack:
Attack Transactions Explained
Dangerous fallback function using delegatecall
The Parity Wallet Code
Delegate Chapter Summary
Delegate References:
Chapter 11 - Look into My Crystal Ball: Bad Randomness Issues
Cryptographic Implementations and Predictable PRNGs
Simple BlockHash Example
Hands on Lab - BlockHash Vulnerability Walk and Talk
Exam Prep - DApp Target + Detailed Lab Guide
Preventing Randomness Issues
Bad Randomness Summary
Bad Randomness References
Chapter 12 - Automated Static Application Security Testing
Content - Not written - Up Next
Hands On Lab - Not written - Up Next
Summary Not written - Up Next
References - Not written - Up Next
Chapter 13 - CTF Exam
Final Exam and CTF Certification Exam Target
Final Exam Reporting
Appendices:
Appendix I – Pre-Requisite Suggestions:
Programming Pre-Requisites:
Web Application Hacking Pre-Requisites:
Appendix II – Other Blockchain Learning Resources and Certifications
Appendix III – Non-Exhaustive Scoping Questions
Appendix IV – Non-Exhaustive List of things to check for
Related articles
- Pentest Tools Download
- Pentest Tools Find Subdomains
- Nsa Hack Tools
- Hack Tools For Mac
- Pentest Tools Online
- Hack Tools For Pc
- New Hacker Tools
- Hack Tool Apk No Root
- Hacking Tools Online
- Hack Tools
- Nsa Hack Tools
- Hacker Tools Windows
- Pentest Tools For Ubuntu
- Best Hacking Tools 2019
- New Hack Tools
- How To Hack
- Hack Website Online Tool
- Hacker Tools Github
- Hacking Tools For Windows
- New Hack Tools
- Usb Pentest Tools
- Termux Hacking Tools 2019
- Bluetooth Hacking Tools Kali
- Best Hacking Tools 2020
- What Are Hacking Tools
- How To Hack
- New Hack Tools
- Hacking Tools For Kali Linux
- Hack Tools Pc
- Black Hat Hacker Tools
- Pentest Automation Tools
- Pentest Tools Free
- Termux Hacking Tools 2019
- Hacking Tools Hardware
- Game Hacking
- Hacking Tools
- Hack Tool Apk No Root
- Hacking Tools Mac
- Kik Hack Tools
- Pentest Tools Android
- Hack Tools For Games
- Install Pentest Tools Ubuntu
- Hack Tools
- Hacker Search Tools
- Tools 4 Hack
- Blackhat Hacker Tools
- New Hack Tools
- Hacker Tools Free
- Hacker Tools 2019
- Termux Hacking Tools 2019
- Best Hacking Tools 2019
- Hacking Tools For Windows Free Download
- Hacker Tools Linux
- Pentest Tools
- Hacker Tools For Ios
- Hacking Tools For Beginners
- Nsa Hack Tools
- What Are Hacking Tools
- Hacker Tools Free Download
- Hacking Tools Kit
- Github Hacking Tools
- Hacking Tools Usb
- Hacks And Tools
- Pentest Tools Framework
- Hacking Tools Name
- Hacking Tools Hardware
- How To Make Hacking Tools
- Tools For Hacker
- Pentest Tools For Android
- Hack Tools Download
- Hacking Tools Windows
- Pentest Tools Alternative
- Hack Tools Mac
- Top Pentest Tools
- Tools 4 Hack
- Hacker Tools Hardware
- Hack Tools Online
- Hacking Tools For Kali Linux
- Hacker Security Tools
- Hack Rom Tools
- Hacking Tools For Mac
- Pentest Tools Url Fuzzer
- Top Pentest Tools
- Hack Tools Pc
- How To Hack
- Wifi Hacker Tools For Windows
- Hacker Tools 2019
DOS (Denial Of Service) Attack Tutorial Ping Of Death ;DDOS
What is DoS Attack?
DOS is an attack used to deny legitimate users access to a resource such as accessing a website, network, emails, etc. or making it extremely slow. DoS is the acronym for Denial of Service. This type of attack is usually implemented by hitting the target resource such as a web server with too many requests at the same time. This results in the server failing to respond to all the requests. The effect of this can either be crashing the servers or slowing them down.
Cutting off some business from the internet can lead to significant loss of business or money. The internet and computer networks power a lot of businesses. Some organizations such as payment gateways, e-commerce sites entirely depend on the internet to do business.
In this tutorial, we will introduce you to what denial of service attack is, how it is performed and how you can protect against such attacks.
Topics covered in this tutorial
- Types of Dos Attacks
- How DoS attacks work
- DoS attack tools
- DoS Protection: Prevent an attack
- Hacking Activity: Ping of Death
- Hacking Activity: Launch a DOS attack
Types of Dos Attacks
There are two types of Dos attacks namely;
- DoS– this type of attack is performed by a single host
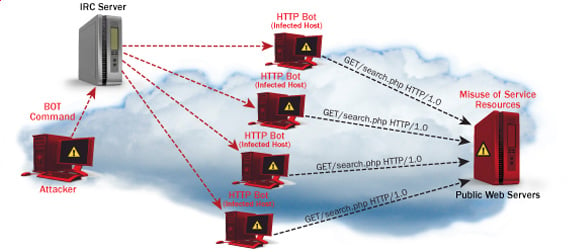
- Distributed DoS– this type of attack is performed by a number of compromised machines that all target the same victim. It floods the network with data packets.
How DoS attacks work
Let's look at how DoS attacks are performed and the techniques used. We will look at five common types of attacks.
Ping of Death
The ping command is usually used to test the availability of a network resource. It works by sending small data packets to the network resource. The ping of death takes advantage of this and sends data packets above the maximum limit (65,536 bytes) that TCP/IP allows. TCP/IP fragmentation breaks the packets into small chunks that are sent to the server. Since the sent data packages are larger than what the server can handle, the server can freeze, reboot, or crash.
Smurf
This type of attack uses large amounts of Internet Control Message Protocol (ICMP) ping traffic target at an Internet Broadcast Address. The reply IP address is spoofed to that of the intended victim. All the replies are sent to the victim instead of the IP used for the pings. Since a single Internet Broadcast Address can support a maximum of 255 hosts, a smurf attack amplifies a single ping 255 times. The effect of this is slowing down the network to a point where it is impossible to use it.
Buffer overflow
A buffer is a temporal storage location in RAM that is used to hold data so that the CPU can manipulate it before writing it back to the disc. Buffers have a size limit. This type of attack loads the buffer with more data that it can hold. This causes the buffer to overflow and corrupt the data it holds. An example of a buffer overflow is sending emails with file names that have 256 characters.
Teardrop
This type of attack uses larger data packets. TCP/IP breaks them into fragments that are assembled on the receiving host. The attacker manipulates the packets as they are sent so that they overlap each other. This can cause the intended victim to crash as it tries to re-assemble the packets.
SYN attack
SYN is a short form for Synchronize. This type of attack takes advantage of the three-way handshake to establish communication using TCP. SYN attack works by flooding the victim with incomplete SYN messages. This causes the victim machine to allocate memory resources that are never used and deny access to legitimate users.
DoS attack tools
The following are some of the tools that can be used to perform DoS attacks.
- Nemesy– this tool can be used to generate random packets. It works on windows. This tool can be downloaded from http://packetstormsecurity.com/files/25599/nemesy13.zip.html . Due to the nature of the program, if you have an antivirus, it will most likely be detected as a virus.
- Land and LaTierra– this tool can be used for IP spoofing and opening TCP connections
- Blast– this tool can be downloaded from http://www.opencomm.co.uk/products/blast/features.php
- Panther- this tool can be used to flood a victim's network with UDP packets.
- Botnets– these are multitudes of compromised computers on the Internet that can be used to perform a distributed denial of service attack.
DoS Protection: Prevent an attack
An organization can adopt the following policy to protect itself against Denial of Service attacks.
- Attacks such as SYN flooding take advantage of bugs in the operating system. Installing security patches can help reduce the chances of such attacks.
- Intrusion detection systems can also be used to identify and even stop illegal activities
- Firewalls can be used to stop simple DoS attacks by blocking all traffic coming from an attacker by identifying his IP.
- Routers can be configured via the Access Control List to limit access to the network and drop suspected illegal traffic.
Hacking Activity: Ping of Death
We will assume you are using Windows for this exercise. We will also assume that you have at least two computers that are on the same network. DOS attacks are illegal on networks that you are not authorized to do so. This is why you will need to setup your own network for this exercise.
Open the command prompt on the target computer
Enter the command ipconfig. You will get results similar to the ones shown below
For this example, we are using Mobile Broadband connection details. Take note of the IP address. Note: for this example to be more effective, and you must use a LAN network.
Switch to the computer that you want to use for the attack and open the command prompt
We will ping our victim computer with infinite data packets of 65500
Enter the following command
ping 10.128.131.108 –t |65500
HERE,
- "ping" sends the data packets to the victim
- "10.128.131.108" is the IP address of the victim
- "-t" means the data packets should be sent until the program is stopped
- "-l" specifies the data load to be sent to the victim
You will get results similar to the ones shown below
Flooding the target computer with data packets doesn't have much effect on the victim. In order for the attack to be more effective, you should attack the target computer with pings from more than one computer.
The above attack can be used to attacker routers, web servers etc.
If you want to see the effects of the attack on the target computer, you can open the task manager and view the network activities.
- Right click on the taskbar
- Select start task manager
- Click on the network tab
- You will get results similar to the following
If the attack is successful, you should be able to see increased network activities.
Hacking Activity: Launch a DOS attack
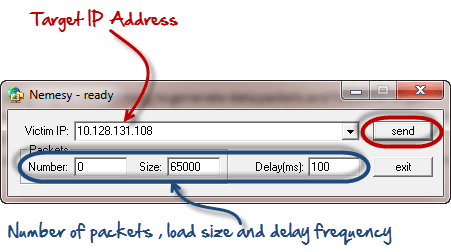
In this practical scenario, we are going to use Nemesy to generate data packets and flood the target computer, router or server.
As stated above, Nemesy will be detected as an illegal program by your anti-virus. You will have to disable the anti-virus for this exercise.
- Download Nemesy from http://packetstormsecurity.com/files/25599/nemesy13.zip.html
- Unzip it and run the program Nemesy.exe
- You will get the following interface
Enter the target IP address, in this example; we have used the target IP we used in the above example.
HERE,
- 0 as the number of packets means infinity. You can set it to the desired number if you do not want to send, infinity data packets
- The size field specifies the data bytes to be sent and the delay specifies the time interval in milliseconds.
Click on send button
You should be able to see the following results
The title bar will show you the number of packets sent
Click on halt button to stop the program from sending data packets.
You can monitor the task manager of the target computer to see the network activities.
Summary
- A denial of service attack's intent is to deny legitimate users access to a resource such as a network, server etc.
- There are two types of attacks, denial of service and distributed denial of service.
- A denial of service attack can be carried out using SYN Flooding, Ping of Death, Teardrop, Smurf or buffer overflow
- Security patches for operating systems, router configuration, firewalls and intrusion detection systems can be used to protect against denial of service attacks.
- Hacker Tools Apk
- Hacking Tools Mac
- Hacker Tools
- Physical Pentest Tools
- Pentest Tools Tcp Port Scanner
- Pentest Reporting Tools
- Hacking App
- Hack Tools For Ubuntu
- Hacking Tools Software
- Hacking Tools For Kali Linux
- Pentest Tools For Android
- Pentest Tools For Mac
- Pentest Tools Github
- Beginner Hacker Tools
- Top Pentest Tools
- Pentest Tools For Windows
- New Hack Tools
- Hacking Tools For Windows
- Hackers Toolbox
- How To Make Hacking Tools
- Hacker Tools Software
- Pentest Tools Framework
- Hacking Tools Windows 10
- Pentest Tools Framework
- Pentest Tools Review
- Underground Hacker Sites
- Pentest Tools Framework
- How To Make Hacking Tools
- Tools 4 Hack
- Pentest Tools Download
- Hacker Tools
- Hack Tool Apk
- Hacking Tools Download
- Hacker Tools Mac
- Pentest Box Tools Download
- Pentest Tools Windows
- Hacker
- Ethical Hacker Tools
- Hack Website Online Tool
- Hacking Tools For Mac
- Tools 4 Hack
- Hacking Tools And Software
- Wifi Hacker Tools For Windows
- How To Install Pentest Tools In Ubuntu
- Hack Tools
- Pentest Tools Open Source
- Computer Hacker
- Hacking Tools For Beginners
- Hacker Tools Free
- Easy Hack Tools
- Hack Tools For Pc
- Hacking Tools For Kali Linux
- Hacking App
- Hack Tool Apk No Root
- Hacking Tools Mac
- Hacker Search Tools
- Hacker Tools Apk
- Hak5 Tools
- Pentest Tools Tcp Port Scanner
- Pentest Tools For Mac
- Hacker Tools List
- Beginner Hacker Tools
- Github Hacking Tools
- What Is Hacking Tools
- Termux Hacking Tools 2019
- Hack Tools 2019
- Hacking Tools For Kali Linux
- Nsa Hack Tools Download
- Hacker Tools Software
- Best Pentesting Tools 2018
- Hackers Toolbox
- Hacking Tools Online
- Hacking Tools 2019
- Kik Hack Tools
- Hak5 Tools
- Hacker Tools Hardware
- Hacker Tools Mac
- Hacking Tools 2020
- Hacker Tools Linux
- Hacking Tools For Beginners
- Hack Tools Mac
- Hackrf Tools
- How To Make Hacking Tools
- Computer Hacker
- Hacker Tools Mac
- Hacker Tools For Ios
- Github Hacking Tools
- Nsa Hack Tools Download
- Hack Tools Download
- Hack Website Online Tool
- Hacking Tools For Pc
- Hacker Tools Mac
- Hack Tools Online
- Pentest Tools Review
- Hacking Tools And Software
- Hacker Tools 2020
- Hack Tools Download
- Pentest Tools Github
- Hack Tools Pc
- Hack Tools For Ubuntu
- New Hacker Tools
- Hack Tools Mac
- New Hacker Tools
- Hacker Tools List
- New Hack Tools
- Hacker Techniques Tools And Incident Handling
- Hak5 Tools
- Hack Apps
- Pentest Tools Bluekeep
- Pentest Box Tools Download
- Hacker Techniques Tools And Incident Handling
- Best Hacking Tools 2019